Domination of these 5 algorithms over the world4 min read
The algorithm is everywhere, it’s science. If you want to become a developer, have a taste about the algorithm in the very beginning is crucial. It is used a lot in game programming, web programming to deep learning, AI, etc…When trying to solve a problem, it teaches us how to use our brain and find out the most effective way to solve that trouble. As a result, algorithms are interesting because they train us how to think like a real programmer.
So what is the algorithm?
In mathematics and computer science, an algorithm is an unambiguous specification of how to solve a class of problems. Algorithms can perform calculation, data processing and automated reasoning tasks.
Informally, an algorithm is any well-defined computational procedure that takes
some value, or set of values, as input and produces some value, or set of values, as
output. An algorithm is thus a sequence of computational steps that transform the
input into the output.
But in the concise and understandable talk, an algorithm is the procedure that we define to solve a particular problem.
Here are the top 5 algorithms that dominate our world…
1. Merge Sort, Quick Sort and Heap Sort
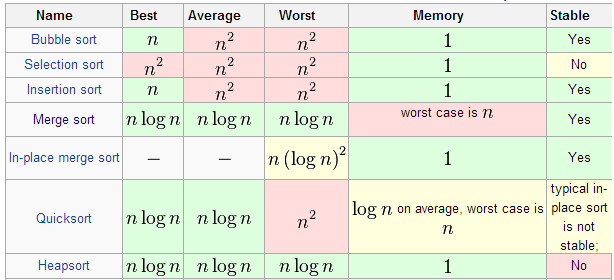
What is the best algorithm to sort elements? It depends on what you need, and that’s why I put the three more frequently used sort algorithms in the same place; maybe you have a preference for one, but all of them are equally important.
The Merge Sort algorithm is by far one of the most important algorithms that we have today. It is a comparison-based sorting algorithm that uses the divide-and-conquer approach to solve a problem that once was a 0(n^2). It was invented by the mathematician John von Neumann in 1945,
QuickSort is a different approach to the sorting problem, it can use in-place partition algorithms and is a divide and conquer algorithm as well. The problem with this algorithm is that is not a stable sort but is really efficient for sorting RAM-based arrays.
Finally, Heap Sort algorithm uses a priority queue that reduces the search time in the data. This algorithm is also an in-place algorithm and is not a stable sort.
These algorithms are a big improvement over other approaches previously used as the bubble sort, in fact, it is thanks to them that today we have Data mining, artificial intelligence, link analysis and the most of the computing tools in the world including the web.
2. Fourier Transform and Fast Fourier Transform
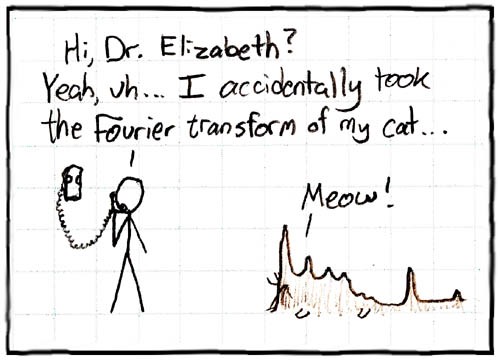
Our entire digital world uses these simple but really powerful algorithms, which transform signals from their time domain into their frequency domain and vice versa. In fact, you are seeing this post thanks to these algorithms.
The internet, your WiFi, smartphone, phone, computer, router, satellites, almost everything that has a computer inside use these algorithms in one way or another to function. You can’t get a degree in electronics, computing or telecommunications without studying these important algorithms.
3. Dijkstra’s algorithm
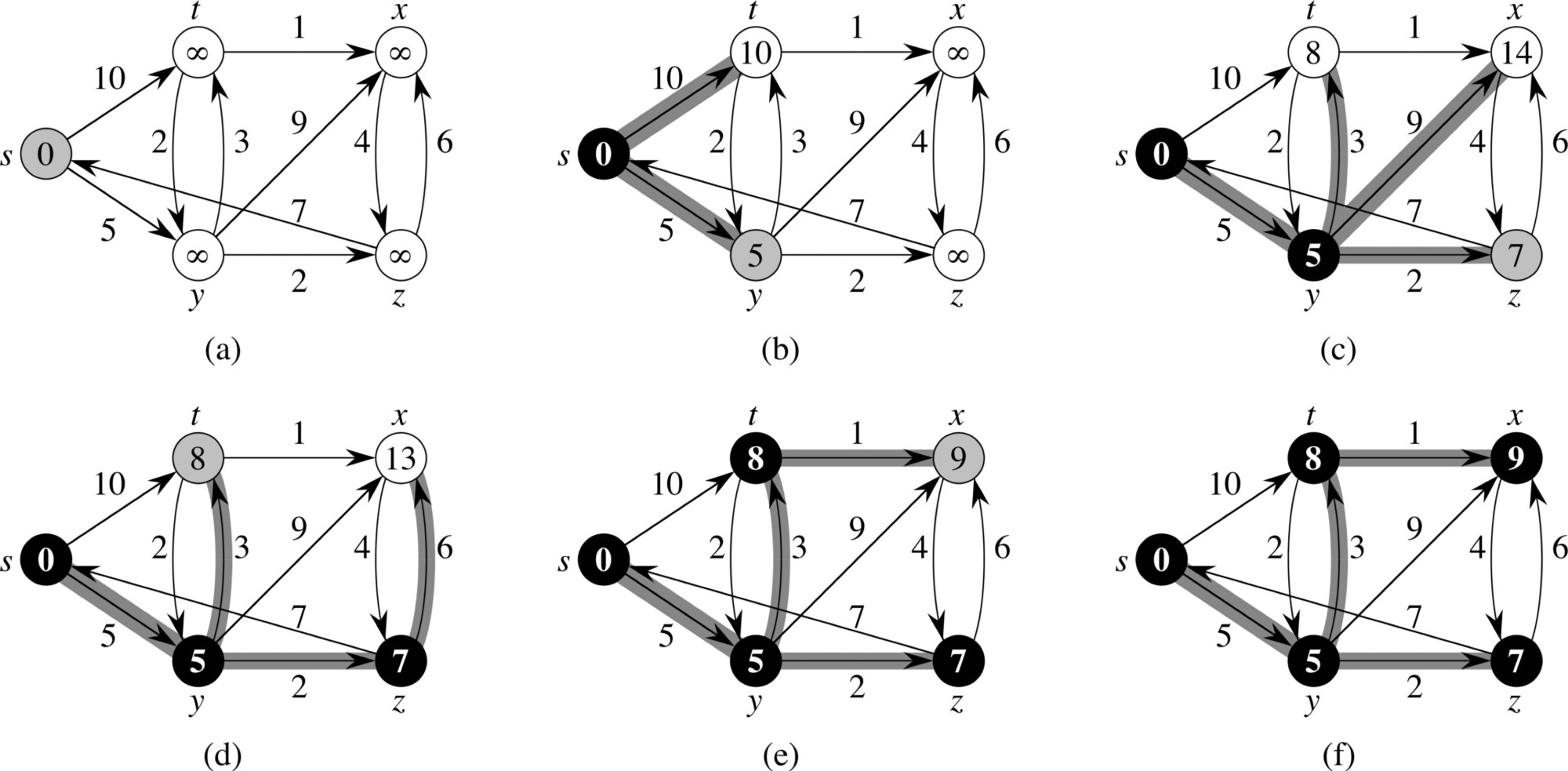
It is not crazy to say that the internet wouldn’t work as efficiently as it does if it wasn’t because of this algorithm. This graph search algorithm is used in different applications where the problem can be modeled as a graph and you have to find the shortest path between two nodes.
Today, even when we have better solutions to the problem of finding the shortest path, Dijkstra’s algorithm is still used in systems that require stability.
4. RSA algorithm
The internet wouldn’t be as important as it is today if it wasn’t for cryptography and cybersecurity. You can think “Sure, security in the era of NSA and other intelligence agencies” or “You have to be really naive to think you are safe on the Internet”; but, people need to feel that they are secure in order to spend their money. After all, you wouldn’t input your credit card number on a web service if you know it is not secure.
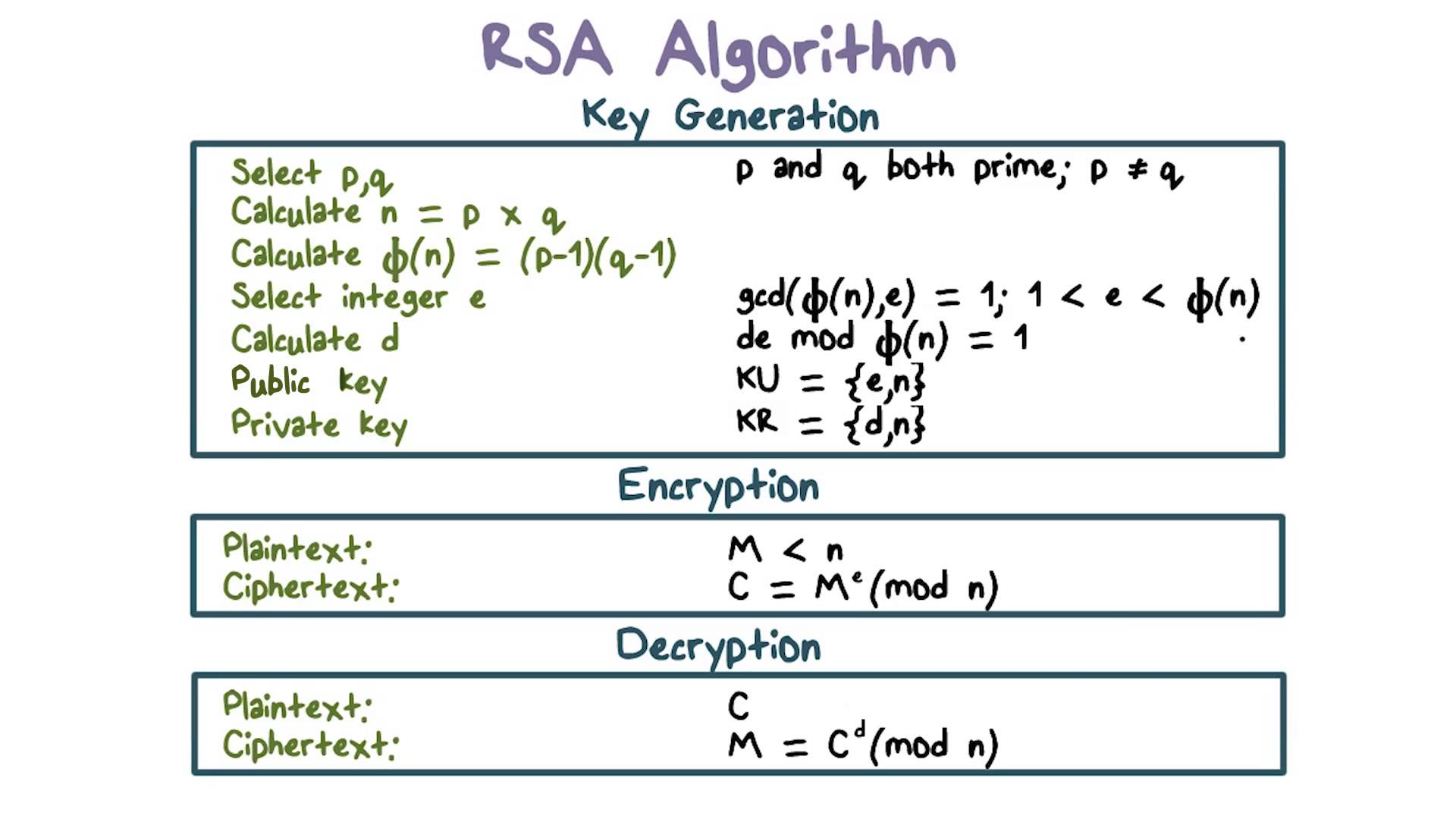
And from the field of cryptography, there is an algorithm that remains one of the most important in the world: the RSA algorithm. Developed by the founders of the company RSA, this algorithm made cryptography available to everybody in the world and helped to shape how cryptography works today. The RSA algorithm is a solution to a simple but complex problem: how to share public keys between independent platforms and final users, in order to allow cryptography (I would argue that it hasn’t been completely solved, I think we need more work in this direction) .
5. Secure Hash Algorithm

This isn’t exactly an algorithm but a family of cryptographic hash functions developed by the NIST in the USA. But this family of algorithms is fundamental for the functioning of the World. From your app store, your email, your antivirus, to your browser, etc , all of them use these algorithms (in reality the hash that results from them) to determine if you have downloaded what you wanted or if you have been the victim of a man in the middle attack or maybe a phishing attack.